When engineers discuss electric vehicle (EV) DC fast chargers, the technical conversation naturally gravitates toward power electronics—wide-bandgap semiconductors, thermal management, thermal resistance, and high-efficiency power conversion topologies. However, as charging infrastructure rapidly evolves into a globally connected, decentralized energy network, a new engineering challenge has emerged at the absolute forefront: cybersecurity and data integrity. Modern fast charging piles are no longer just sophisticated AC-DC converters; they are highly critical Internet of Things (IoT) edge nodes handling sensitive financial transactions, grid-level power dispatching, and bidirectional vehicle-to-grid (V2G) communication.
At the heart of this transformation is the control layer. To guarantee the integrity, safety, and reliability of the EV charging network, hardware-level security is non-negotiable. This article goes beyond power electronics to explore the control hierarchy, specifically focusing on how modern automotive microcontrollers—such as Infineon’s AURIX™ family—equipped with an embedded Hardware Security Module (HSM) act as the ultimate security control hub for fast charging stations. We will conduct a deep technical analysis of how this architecture handles secure service billing, authenticates Over-The-Air (OTA) software upgrades, and prevents the installation of counterfeit components.
Beyond Power Electronics: The Critical Vulnerabilities of Connected Charging
In a traditional electronic design paradigm, the primary focus is on maximizing efficiency and power density. Power engineers meticulously select insulated-gate bipolar transistors (IGBTs) or Silicon Carbide (SiC) MOSFETs to optimize switching losses, a design philosophy extensively covered in technical resources like Designing 150kW DC Fast Chargers with 1200V IGBTs. Yet, unparalleled power density and ultra-low switching losses are ultimately rendered meaningless if the control logic dictating that power delivery can be remotely compromised.
Electric Vehicle Supply Equipment (EVSE) interfaces with multiple external domains simultaneously: the electric vehicle via the charging cable (using protocols like Powerline Communication), the backend central management system via cellular or Ethernet network connections, and the local smart grid infrastructure. Each of these interfaces represents a potential attack vector. If a malicious actor gains access to the MCU controlling the charger, the consequences extend far beyond a single broken machine. The engineering risks include:
- Energy Theft and Billing Fraud: Manipulating the metering data to bypass payment gateways, spoofing vehicle identities to charge external billing accounts illegally, or manipulating the data transferred to the central server.
- Grid Instability: Coordinating a synchronized cyberattack on a vast network of high-power chargers, forcing them to simultaneously draw peak load. Pulling hundreds of megawatts instantly could trigger localized transformer failures or wider grid blackouts.
- Safety Mechanism Bypass: Disabling critical software-level safety limits, such as overvoltage (Vmax), overcurrent (Imax), or thermal shutdown thresholds, leading to catastrophic hardware failure, battery damage, or fire hazards.
To mitigate these severe risks, traditional software-based encryption is entirely insufficient. Operating systems and application software are inherently vulnerable to zero-day exploits, buffer overflows, and privilege escalation. The industry standard has therefore firmly shifted to hardware-based security anchors, where cryptographic keys and execution logic are physically isolated at the silicon layer.
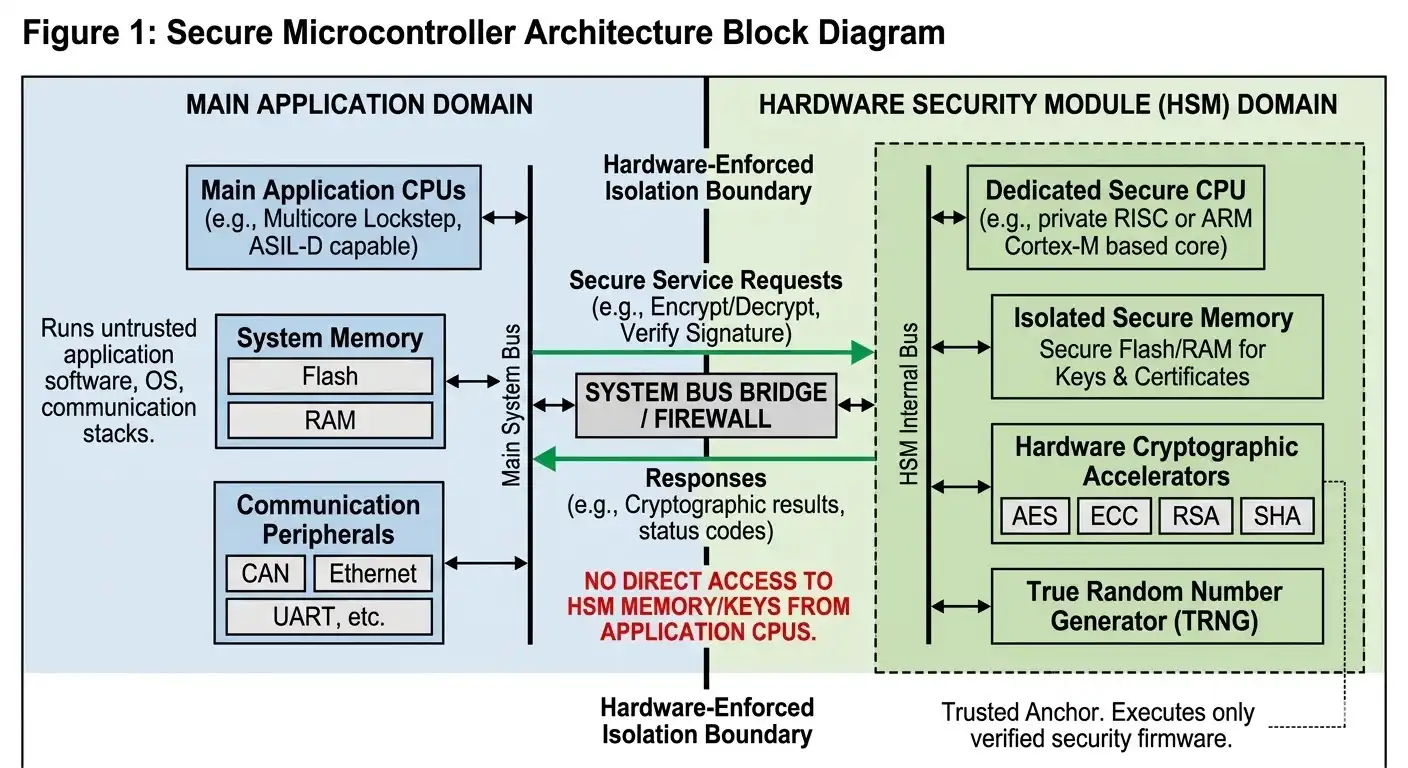
Figure 1: High-level block diagram of a secure microcontroller architecture, illustrating the physical and logical isolation of the Hardware Security Module (HSM) from the main application processing cores.
The Core of Hardware Encryption: Understanding the HSM Architecture
High-end control hubs, typified by the AURIX™ multicore architecture, are engineered specifically for safety-critical automotive and industrial applications. While their lockstep processing cores provide ASIL-D (Automotive Safety Integrity Level D) functional safety compliant with ISO 26262, their formidable security posture stems directly from the embedded Hardware Security Module (HSM).
An HSM is essentially an independent, highly secure microcomputer embedded within the main microcontroller die. It operates as a distinct, isolated subsystem. The internal architecture of a standard HSM includes:
- A Private Execution CPU: The HSM utilizes its own dedicated processor that executes security-critical code independently of the main application CPUs. This prevents application-layer malware from interrupting security tasks.
- Isolated Secure Memory: It features dedicated static random-access memory (SRAM) and non-volatile flash memory designed specifically for storing cryptographic keys, digital certificates, and trusted boot code. The main CPU cannot read from or write to this memory space directly; it can only request cryptographic services via a tightly controlled, hardware-enforced bridge.
- Hardware Cryptographic Accelerators: To process complex encryption algorithms without introducing system latency, the HSM contains dedicated hardware logic engines for Advanced Encryption Standard (AES), Elliptic Curve Cryptography (ECC), Rivest-Shamir-Adleman (RSA), and Secure Hash Algorithms (SHA).
- True Random Number Generator (TRNG): A vital physical component that generates unpredictable cryptographic keys based on actual physical entropy (e.g., thermal noise), rather than relying on vulnerable algorithmic pseudo-randomness.
This strict physical silicon segregation ensures that even if a hacker completely compromises the operating system running on the main processing cores, they absolutely cannot extract the private cryptographic keys stored inside the HSM. The private keys literally never leave the secure silicon enclave.
Pillar 1: ISO 15118 “Plug & Charge” Authentication and Secure Billing
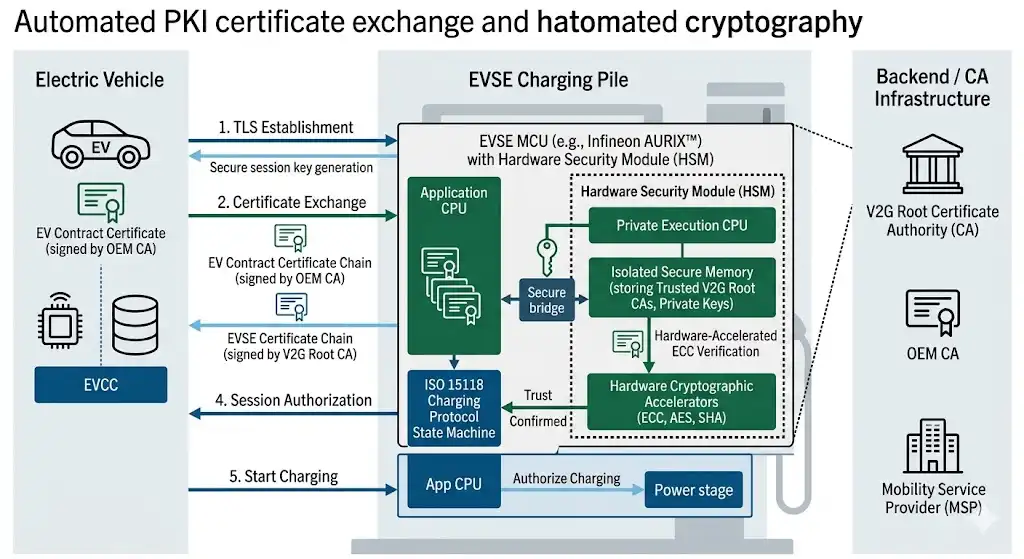
The user experience of modern EV charging is rapidly migrating toward a seamless, automated methodology known as “Plug & Charge,” heavily defined by the ISO 15118 international standard. Under this framework, the driver simply connects the charging cable to the vehicle; the car and the EVSE automatically mutually authenticate, authorize the charging session, and process the financial billing without the need for external RFID cards, credit card readers, or mobile applications.
This automated, frictionless billing requires an incredibly robust Public Key Infrastructure (PKI) ecosystem. When the EV connects to the charger, a Transport Layer Security (TLS) session must be established over the HomePlug Green PHY Powerline Communication (PLC) link. This initial handshake involves the rapid exchange and verification of multiple digital certificates belonging to the vehicle, the charger, and the mobility service provider.
The hardware HSM is the critical enabler here. During the TLS handshake, asymmetric cryptography (such as ECC) is utilized to establish a shared secret key, which is subsequently used for symmetric encryption (such as AES) for the remainder of the session. If the main application CPU were forced to handle these cryptographic operations in software, the processing latency could disrupt the strict timing requirements of the charging protocol. Furthermore, the private keys would be temporarily exposed in the system’s general RAM, leaving them vulnerable to memory-scraping attacks.
Instead, the main CPU passes the encrypted data payload directly to the HSM. The HSM’s hardware accelerators perform the complex ECC mathematics internally, verify the vehicle’s digital certificate against trusted root certificates stored in its secure flash, and securely negotiate the session keys. This hardware-accelerated process ensures that billing data—including user identification tokens and metered energy (measured in kWh)—cannot be intercepted, cloned, or spoofed by malicious third parties.
Pillar 2: Ironclad Firmware OTA Updates and Secure Boot
Because charging communication protocols, backend grid compliance codes, and active cybersecurity threats are constantly evolving, EV fast chargers require frequent firmware updates to maintain operability. Executing these Over-The-Air (OTA) updates introduces a severe system vulnerability: how does the charging controller verify that the incoming software update is genuinely from the original equipment manufacturer (OEM) and not a destructive payload injected by a hacker?
Advanced security MCUs solve this dilemma through two rigidly enforced, interconnected mechanisms: Secure Boot and Secure OTA Authentication.
The Hardware Secure Boot Process
Whenever the charging station powers on or undergoes a reset, the silicon must establish a definitive “Root of Trust.” Before the main TriCore™ or ARM processing CPUs are permitted to execute the primary operating system or control algorithms, the HSM wakes up first. The HSM immediately calculates a cryptographic hash (typically using SHA-256 or SHA-384) of the bootloader and the primary application code residing in the system’s flash memory.
It then compares this calculated mathematical hash against a trusted, digitally signed hash securely stored within the HSM’s immutable memory during manufacturing. If the two values perfectly match, the HSM signals the hardware that the code is authentic and untampered, allowing the boot sequence to proceed normally. If even a single bit of the application code has been altered—for instance, if a hacker injected a backdoor into the memory—the hash will fail to match. The HSM will immediately halt the boot process, lock the execution cores, and force the charger into a safe, non-operational error state.
Authenticating OTA Firmware Upgrades
When a new firmware package is downloaded over the cellular network, it arrives fully encrypted and digitally signed with the manufacturer’s private key. The main CPU is not authorized to apply this update directly. It must pass the encrypted package to the HSM.
The HSM utilizes the manufacturer’s public key (hardcoded into the HSM during initial production) to verify the digital signature of the incoming update. Once the origin and the structural integrity of the software are cryptographically proven, the HSM decrypts the payload and authorizes the main CPU to write the new instructions into the flash memory. This strictly gated mechanism ensures that only authorized, thoroughly tested engineering code is ever permitted to execute on the power electronics control board.
Pillar 3: Anti-Counterfeit Component Identification and Supply Chain Integrity
High-power DC fast chargers—especially ultra-fast systems capable of 150 kW to 350 kW outputs—are highly modular hardware systems. They are composed of multiple distinct power conversion modules, liquid cooling pumps, sophisticated smart meters, and human-machine interface (HMI) displays. The electronic engineering underlying these internal sub-systems is complex, as extensively detailed in The Vienna Rectifier: Engineering the Backbone of 150 kW EV Charging Infrastructure.
Due to the high capital cost of these modular sub-systems, a lucrative grey market for counterfeit or uncertified replacement parts exists. Installing a substandard power module or a counterfeit cooling fan into a high-voltage, high-current system can result in catastrophic thermal events, destroying the entire charging pile and potentially endangering operators.
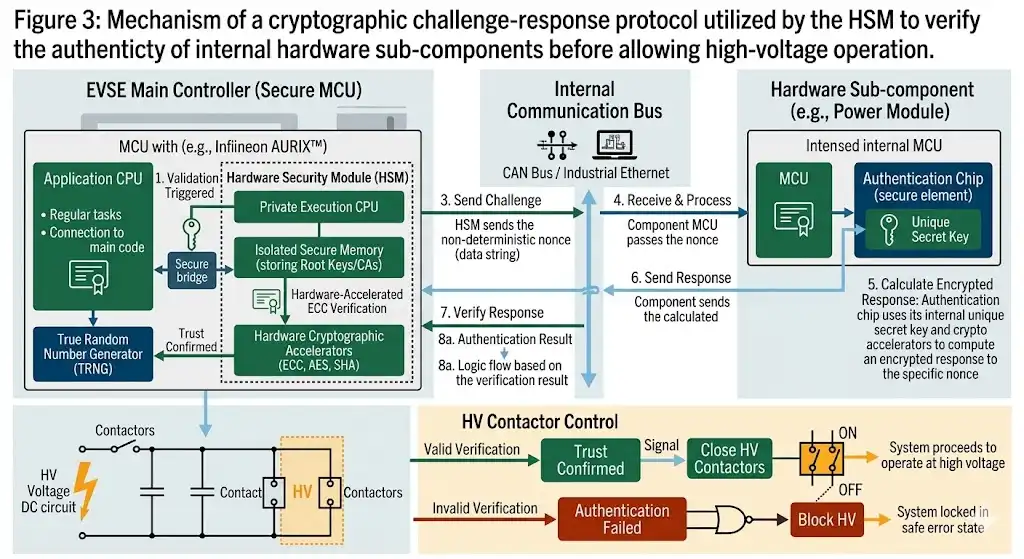
To rigorously maintain supply chain integrity and operational safety, the control layer must actively authenticate every single hardware module connected to the internal communication bus (such as the internal CAN bus or Industrial Ethernet). The HSM enables robust anti-counterfeit component identification through cryptographic “challenge-response” protocols.
When a maintenance technician plugs a new sub-module into the charger, the main MCU sends a cryptographically generated “challenge” (a highly random string of data) to a small, inexpensive authentication chip located on the new sub-module. The sub-module must encrypt this specific challenge using its unique, factory-programmed secret key and transmit the “response” back to the main MCU. The main MCU passes this to the HSM, which evaluates the cryptographic response. If the response is mathematically valid, the HSM confirms that the component is an original, manufacturer-certified OEM part.
If the hardware authentication fails, the control system executes predefined protective actions. It will typically refuse to close the main high-voltage contactors, register a severe security error code in the backend maintenance database, or force the charger to operate in a severely derated state (e.g., strictly limiting the charging output to 50 kW instead of 350 kW) to prevent electrically stressing the unverified, potentially dangerous component.
The Intersection of Cyber Security and Power Electronics Control
While we have conceptually separated the control layer from the power layer for the sake of analytical clarity, in a real-world EVSE system, the two are inextricably linked. The secure microcontroller is directly responsible for generating the high-frequency Pulse Width Modulation (PWM) signals that drive the gates of the IGBTs or SiC MOSFETs in the power stage.
If the precise microsecond timing of these PWM signals is disrupted by a cyberattack or a software glitch caused by unauthorized malicious code, it can easily lead to short-circuit shoot-through conditions. This instantly destroys the power semiconductors, where peak output current (Iout) and operating DC bus voltage (VDC) are highly sensitive to any control timing anomalies. By utilizing a secure hardware architecture, engineers ensure that the fundamental control loop operating the power devices remains completely isolated from external software manipulation.
Furthermore, advanced field diagnostics and hardware failure analysis rely heavily on the accuracy of the system data logs. When power engineers analyze catastrophic field failures—a highly technical process explored in IGBT Failure Analysis: Preventing Overcurrent, Overvoltage, and Overtemperature—they depend entirely on the telemetry data recorded by the MCU prior to the failure. The HSM can digitally sign these critical fault logs, guaranteeing that the forensic diagnostic data sent back to the engineering team is 100% accurate and has not been maliciously altered to mask the true root cause of a failure or cover up a cyber intrusion.
Bridging the Gap: From Secure Control to High-Power Execution
While the AURIX™ MCU and its embedded HSM provide the impenetrable logic core for EVSE cybersecurity, these precisely encrypted control signals must ultimately drive highly robust power semiconductors. The exact microsecond timing of the PWM signals generated by the secure control layer dictates the switching of high-power IGBT modules. For modern 150 kW to 350 kW DC fast chargers, selecting the right power stage is as critical as securing the data layer. Engineers frequently rely on industry-standard 1200 V and 1700 V modules to handle the immense electrical and thermal loads:
- For standard 150 kW to 200 kW architectures: The Mitsubishi CM600DX-24T (1200 V, 600 A) is a highly reliable 6th-generation NX series half-bridge module. It offers the exceptional thermal cycling capability required for the continuous high-current demands and frequent load variations of public charging stations.
- For next-generation 800 V and 1000 V ultra-fast charging platforms: As electric vehicle DC bus voltages increase to shorten charging times, standard 1200 V components often lose their necessary voltage derating margin. The Infineon FS450R17KE3 (1700 V, 450 A) provides the essential voltage blocking capability and ruggedness to execute the control layer’s commands safely in extreme high-voltage environments.
By pairing an uncompromisable hardware security hub at the logic level with these heavily ruggedized power modules at the execution level, designers ensure that the charging pile is both digitally secure against cyber threats and electrically invincible against thermal and overcurrent stresses.
Conclusion: Engineering Absolute Trust in the Grid Network
The aggressive proliferation of high-power DC fast charging infrastructure is the fundamental linchpin of the global electric vehicle transition. However, the long-term success of this critical infrastructure relies not just on how fast it can transfer energy from the grid to the battery, but on how securely it can manage data, verify physical identities, and decisively protect against malicious interference.
By elevating the engineering discussion beyond pure power electronics and focusing intently on the control layer, we illuminate the indispensable role of advanced, security-focused microcontrollers. Architectures featuring an embedded Hardware Security Module (HSM) represent the absolute gold standard in this engineering domain. By securely accelerating service billing cryptography, enforcing strict OTA firmware authentication, and mathematically verifying the physical integrity of the hardware through robust anti-counterfeit measures, the control MCU acts as the vigilant, uncompromisable sentinel of the charging pile. For electronics engineers, integrating these hardware-level security measures is no longer considered an optional premium upgrade; it is a foundational, non-negotiable requirement for building a safe, reliable, and trustworthy modern energy grid.
